Traditional network boundary defense approaches to file transfers focus on binary “good” versus “bad” decisions. Utilizing firewalls, antivirus, domain blocking and…
Hans-Wilhelm Dünn
By Pressestelle Uncategorized News Events
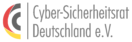
In companies but also in households, security weaknesses in IoT devices such as IP cameras, smart TVs or smart kitchen…